Getty Images
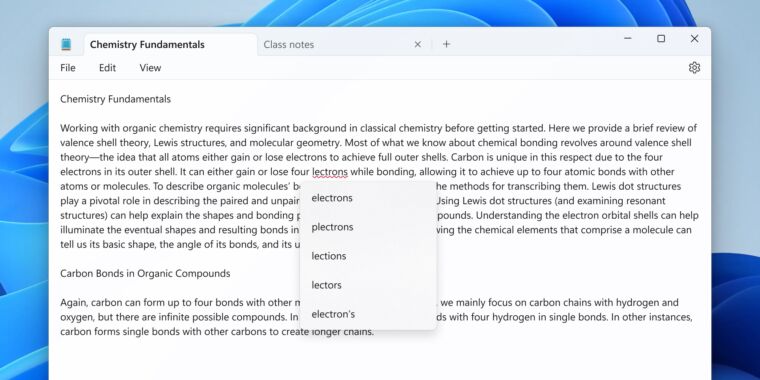
A critical zero-day vulnerability Google reported on Wednesday in its Chrome browser is opening the Internet to a new chapter of Groundhog Day.
Like a critical zero-day Google disclosed on September 11, the new exploited vulnerability doesn’t affect just Chrome. Already, Mozilla has said that its Firefox browser is vulnerable to the same bug, which is tracked as CVE-2023-5217. And just like CVE-2023-4863 from 17 days ago, the new one resides in a widely used code library for processing media files, specifically those in the VP8 format.
Pages here and here list hundreds of packages for Ubuntu and Debian alone that rely on the library known as libvpx. Most browsers use it, and the list of software or vendors supporting it reads like a who’s who of the Internet, including Skype, Adobe, VLC, and Android.
It’s unclear how many software packages that depend on libvpx will be vulnerable to CVE-2023-5217. Google’s disclosure says the zero-day applies to video encoding. By contrast, the zero-day exploited in libwebp, the code library vulnerable to the attacks earlier this month, worked for encoding and decoding. In other words, based on the wording in the disclosure, CVE-2023-5217 requires a targeted device to create media in the VP8 format. CVE-2023-4863 could be exploited when a targeted device simply displayed a booby-trapped image.
“The fact that a package depends on libvpx does NOT necessarily mean that it’d be vulnerable,” Will Dorman, senior principal analyst at Analygence, wrote in an online interview. “The vuln is in VP8 encoding, so if something uses libvpx only for decoding, they have nothing to worry about.” Even with that important distinction, there are likely to be many more packages besides Chrome and Firefox that will require patching. “Firefox, Chrome (and Chromium-based) browsers, plus other things that expose VP8 encoding capabilities from libvpx to JavaScript (i.e. web browsers), seem to be at risk,” he said.
Few details are currently available about the in-the-wild attacks that exploited the latest zero-day. The Google post said only that code exploiting the flaw “exists in the wild.” A social media post from Maddie Stone, a security researcher in Google’s Threat Analysis Group, said the zero-day was “in use by a commercial surveillance vendor.” Google credited Clement Lecigne of Google’s TAG for discovering the vulnerability on Monday, just two days prior to the patch it released on Wednesday.
The zero-day is patched in Chrome 117.0.5938.132, Firefox 118.0.1, Firefox ESR 115.3.1, Firefox Focus for Android 118.1, and Firefox for Android 118.1.
There are other similarities between the two zero-days. They both stem from buffer overflows that allow remote code execution with little or no interaction on the part of an end user other than to visit a malicious webpage. They both affect media libraries that Google published more than a decade ago. And both libraries are written in C, a 50-year-old programming language widely regarded as unsafe because it’s prone to memory-corruption vulnerabilities.
One thing is different this time: The wording in the CVE Google assigned on Wednesday is clear that the vulnerability affects not just Chrome but also libvpx. When Google assigned CVE-2023-4863, it mentioned only that the vulnerability affected Chrome, leading to confusion that critics said slowed patching by other affected software packages.
It will probably take a few more days for the full scope of CVE-2023-5217 to become clear. Project developers for libvpx didn’t immediately answer an email asking if a patched version of the library is available or what specifically is required to exploit software that uses the library. For now, people using apps, software frameworks, or websites that involve VP8, especially for video encoding, should exercise caution.